Use this workflow when running OpenSRE via the localDocumentation Index
Fetch the complete documentation index at: https://opensre.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
opensre binary.
You can work in two ways:
- Interactive prompt shell — run
opensrewith no subcommand (TTY) to enter the REPL: describe incidents conversationally, stream investigations, and use slash commands. - Direct investigation — run
opensre investigatefrom your terminal with-ipointing at an alert payload (or--interactiveto pick a file in the UI). The process runs and exits when the investigation completes.
1) Start an investigation
Interactive shell (opensre)
From a terminal with stdin and stdout attached (opensre detects a TTY), run:
/help for slash commands and /exit when finished.
Direct investigation (opensre investigate)
Pass an alert payload to opensre investigate:
--interactive to pick an input file from your terminal UI.
2) Review investigation artifacts
A local run produces structured RCA artifacts such as:problem.mdfor incident framing and initial hypothesistheory/hypothesis_*.mdfor each hypothesis tested during the runreport.mdfor final root-cause summary and next steps
3) Understand what OpenSRE analyzed
Each run captures:- the original alert payload
- extracted context and normalized evidence
- tool outputs collected from connected integrations
- final diagnosis and recommended remediation steps
Chat
For local binary usage, the primary workflow is file-based (problem.md, report.md, and optional JSON output).
You can open these artifacts in your editor and iterate from there (for example, by asking your editor’s AI chat
to drill into specific hypotheses or evidence sections).
Slack reports
If you’ve configured the Slack integration, OpenSRE can publish a concise incident summary into Slack after the local investigation completes.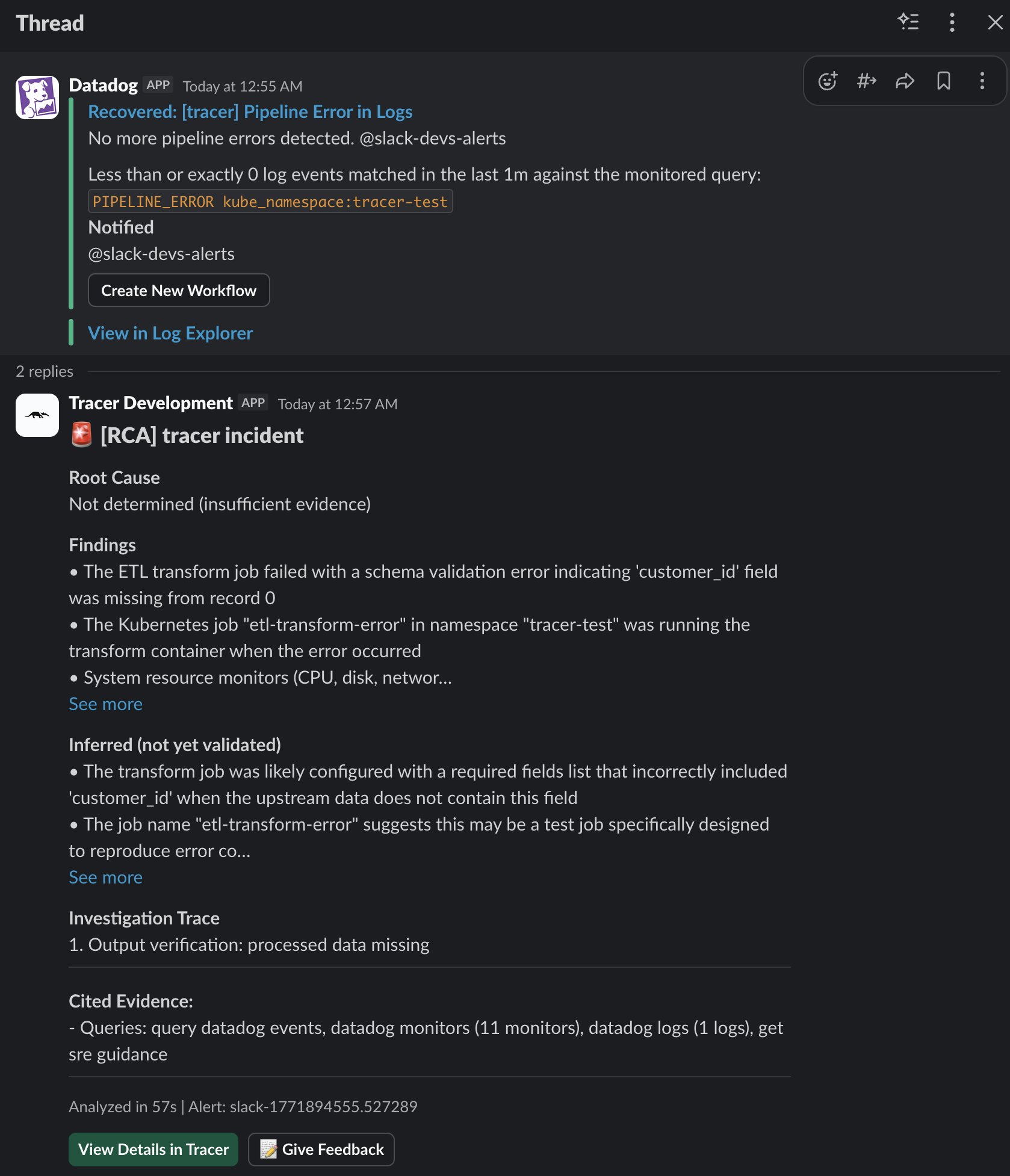


 Tracer
Tracer